Section 16.2 Diffie Hellman key exchange
To initiate secure communication it is sufficient to determine a shared secret in the form of a cryptographic key. This key can be used for communication using a symmetric cryptographic protocol, such as AES, which requires less resources than communicating using a public key protocol. The Diffie-Hellman key exchange is a cryptographic protocol for exchanging cryptographic keys over a public channel. It was proposed by Ralph Merkle [9] and is named after Whitfield Diffie and Martin Hellman [2].
If there is no doubt about the identity of the other party, the Diffie-Hellman key exchange does not need any additional infrastructure, such as a key directory.
To create a shared secret Alice (A) and Bob (B) follow the following steps (also see Figure 16.8). First Alice and Bob agree on the group they want to work in. All powers are to be computed in this group.
- Alice and Bob
- Alice and Bob agree on a prime number \(p\) and a \(g\in\Z_p^\otimes\text{.}\) They will work in \((\Z_p^\otimes,\otimes)\) where \(a\otimes b=(a\cdot b)\fmod p\text{.}\)
- Alice: Secret
-
Alice chooses her secret \(a\text{,}\) uses it to compute her public information \(A\) and sends it to Bob.
- Bob: Secret
-
Bob chooses his secret \(b\text{,}\) uses it to compute his public information \(B\) and sends it to Alice.
- Alice: Shared secret
- Bob: Shared secret
Alice has computed the secret
\begin{equation*}
s_A=\gexp{B}{a}{\otimes}=\gexp{\left(\gexp{g}{b}{\otimes}\right)}{a}{\otimes}=\gexp{g}{(a\cdot b)}{\otimes}\text{.}
\end{equation*}
Bob has computed
\begin{equation*}
s_B=\gexp{A}{b}{\otimes}=\gexp{\left(\gexp{g}{a}{\otimes}\right)}{b}{\otimes}=\gexp{g}{(b\cdot a)}{\otimes}\text{.}
\end{equation*}
Assume Eve has eavesdropped on the communication between Alice and Bob and now knows the \(p\text{,}\) \(g\text{,}\) \(A\text{,}\) and \(B\text{.}\) To obtain the shared secret \(s\text{,}\) Eve needs either Alice’s secret \(a\) or Bob’s secret \(b\text{,}\) which can only be obtained by finding the discrete logarithm of \(A\) to base \(g\) in \((\Z_p^\otimes,\otimes)\) or the discrete logarithm of \(B\) to base \(g\) in \((\Z_p^\otimes,\otimes)\text{.}\) So, the security of the Diffie-Hellman key exchange depends on the difficulty of computing discrete logarithms in \((\Z_p^\otimes,\otimes)\text{.}\)
In the video in Figure 16.9 we summarize what we have just described.
Investigate the dependencies of the steps in the Diffie Hellman key exchange in the interactive Example 16.10.
In Example 16.11 we illustrate how the Diffie-Hellman key exchange works with small numbers. The discrete logarithm problem is solved so quickly with these small numbers that it is very easy to break the encryption.
Example 16.11. Diffie-Hellman with small numbers.
We give an example for a Diffie-Hellman key exchange with small numbers.
- Alice and Bob: Group
- Alice and Bob agree on the prime \(p=11\) and the generator \(g=2\text{.}\) They work in the group \((\Z_{11}^\otimes,\otimes)\) where \(a\otimes b=(a\cdot b)\fmod 11\text{.}\)
- Alice: Secret
- Bob: Secret
- Alice: Shared Secret
-
Alice receives \(B=9\) from Bob.
-
Alice computes the shared secret\(s =\gexp{B}{a}{\otimes}\) \(=\gexp{9}{8}{\otimes}\) \(=\gexp{\left(\gexp{\left(\gexp{9}{2}{\otimes}\right)}{2}{\otimes}\right)}{2}{\otimes}\) \(=\gexp{\left(\gexp{4}{2}{\otimes}\right)}{2}{\otimes}\) \(=\gexp{5}{2}{\otimes}=3 \text{.}\)
-
- Bob: Shared Secret
Now Alice and Bob share the secret \(s=3\text{.}\)
In the video Figure 16.12 we give another example.
From Bob’s perspective a key exchange looks as follows.
Problem 16.13. Shared secret.
Alice and Bob agree to use the prime number \(p=17\) and the generator \(g=5\) for their Diffie-Hellman key exchange. Alice sends Bob \(A=2\text{.}\) Bob chooses the random number \(b=3\text{.}\) What is Alice and Bobs shared secret ?
We demonstrate the importance of random numbers in the Diffie-Hellman key exchange.
Problem 16.14. Bad random numbers.
The software company DH insecurity has implemented the random number generator from Figure 16.16, that is, the random numbers are always 4. Alice and Bob both use software from DH insecurity and Eve knows this. Eve eavesdrops on Bob’s communication when Alice and Bob are agreeing on the prime \(p\) and the generator \(g\text{.}\) She learns that \(p=19\) and \(g=15\text{.}\) So Alice and Bob are working in the subgroup of \((\Z_{19},\otimes)\) generated by \(15\text{.}\) Eve now can find Alice’s and Bob’s shared secret generated by the Diffie Hellman key exchange. What is Alice and Bob’s shared secret ?
Solution.
As the random number generator always returns 4, Alice’s secret \(a\) is 4 and Bob’s secret \(b\) is 4. Thus
\(A=\gexp{g}{a}{\otimes} =\) \(\gexp{15}{4}{\otimes}=\) \(\gexp{\left(\gexp{15}{2}{\otimes}\right)}{2}{\otimes}\) \(= \gexp{(15^2\fmod 19)}{2}{\otimes}\) \(= \gexp{(225\fmod 19)}{2}{\otimes}\) \(= \gexp{16}{2}{\otimes}\) \(= 256\fmod 19=9\)
Alice and Bob’s shared secret is
\(s=\gexp{A}{b}{\otimes}\) \(= \gexp{9}{4}{\otimes}\) \(= \gexp{\left(\gexp{9}{2}{\otimes}\right)}{2}{\otimes}\) \(= \gexp{(81\fmod 19)}{2}{\otimes}\) \(= \gexp{5}{2}{\otimes}\) \(= 25\fmod 19=6
\text{.}\)
To give an idea how large the prime \(p\) should be for the Diffie-Hellman key exchange to be secure, we present an example for a discrete logarithm that was computed in 2014.
Example 16.15. A hard discrete logarithm problem that is not hard enough.
Let \(p\) be the 80 decimal digit (596 digits in base 2) prime above:
\begin{align*}
p= \amp 191147927718986609689229466631454649812986246276667354864188\\
\amp 503638807260703436799058776201365135161278134258296128109200\\
\amp 046702912984568752800330221777752773957404540495707852046983\text{.}
\end{align*}
The group \((\Z_p^\otimes,\otimes)\) is generated by \(g=5\text{,}\) that is \(\Z_p^\otimes=\{5^n\mid n\in\N\}\text{.}\) In 2014 the researchers Cyril Bouvier, Pierrick Gaudry, Laurent Imbert, Hamza Jeljeli, and Emmanuel Thomé announced that they computed the discrete logarithm to base 5 of
\begin{align*}
a= \amp 68188080109582330879868861330998506151774854600403700625797\\
\amp 299927558995162740321112260973638619757922646242302104885437\\
\amp 536745080299248852065080008358309735875192480724496530325927\text{.}
\end{align*}
It took them under 130 core years (that is, on a single core computer it would take that long) on a parallel computing cluster to find the solution
\begin{align*}
n= \amp 138670566126823584879625861326333326312363943825621039220215\\
\amp 583346153783336272559955521970357301302912046310782908659450\\
\amp 758549108092918331352215751346054755216673005939933186397777\text{.}
\end{align*}
They applied the data computed for finding this discrete logarithm in the computation of further discrete logarithms which only required a few hours each.
The example illustrates that a prime number with 180 decimal digits (596 digits in base 2) is too small for cryptographic purposes, because the discrete logarithm problem can be solved in a (relatively) short amount of time, provided enough computation power is available. The commonly recommended size of the prime for the Diffie Hellman key exchange is 2048 base 2 digits.
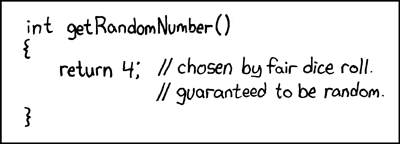
RFC 1149.5 specifies 4 as the standard IEEE-vetted random number.
https://xkcd.com/221)